Threat Modeling is the process of systematically identifying potential security threats, vulnerabilities, and attack vectors that could compromise the confidentiality, integrity, or availability of assets or systems. It involves analyzing the architecture, design, and functionality of a system to anticipate potential threats and proactively implement countermeasures to mitigate risks.
Principles of Threat Modeling
- Proactivity: Threat modeling emphasizes proactive identification and mitigation of security threats before they are exploited by adversaries, enabling organizations to address vulnerabilities early in the development lifecycle.
- Risk-Based Approach: Threat modeling adopts a risk-based approach to prioritize security concerns based on their potential impact and likelihood of occurrence, enabling organizations to focus their resources on addressing the most critical threats.
- Systematic Analysis: Threat modeling involves a systematic analysis of system components, data flows, trust boundaries, and potential attack vectors to identify vulnerabilities and weaknesses that could be exploited by attackers.
- Continuous Improvement: Threat modeling is an iterative process that evolves over time to adapt to changing threats, technologies, and business requirements, enabling organizations to continuously enhance their security posture.
Methodologies of Threat Modeling
- STRIDE: The STRIDE model categorizes threats into six categories: Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege. It helps organizations identify and address security threats based on these categories.
- DREAD: The DREAD model assesses the severity of security threats based on five criteria: Damage potential, Reproducibility, Exploitability, Affected users, and Discoverability. It helps organizations prioritize security issues and allocate resources effectively.
- PASTA: The Process for Attack Simulation and Threat Analysis (PASTA) framework guides organizations through a systematic process of identifying, assessing, and mitigating security threats by analyzing attack scenarios and their potential impact on assets and systems.
- Attack Trees: Attack trees are graphical representations of potential attack scenarios, starting from a root node representing the goal of the attacker and branching out into various attack paths and techniques. They help organizations visualize and analyze potential threats and countermeasures.
Benefits of Threat Modeling
- Risk Mitigation: Threat modeling enables organizations to identify and mitigate security risks and vulnerabilities proactively, reducing the likelihood and impact of security incidents and breaches.
- Cost Savings: By addressing security issues early in the development process, threat modeling helps organizations avoid costly security incidents, compliance violations, and reputation damage associated with security breaches.
- Enhanced Security Awareness: Threat modeling raises awareness of security threats and vulnerabilities among developers, architects, and stakeholders, fostering a culture of security and accountability within organizations.
- Compliance and Regulatory Alignment: Threat modeling helps organizations align with industry regulations, compliance standards, and best practices by identifying and addressing security requirements and controls relevant to their environment.
- Improved Decision-Making: Threat modeling provides valuable insights into the security posture of systems and applications, enabling informed decision-making regarding risk mitigation strategies, resource allocation, and security investments.
Challenges of Threat Modeling
- Complexity: Threat modeling can be complex, especially for large, interconnected systems with diverse architectures, technologies, and attack surfaces. Organizations may struggle to model and analyze all potential threats comprehensively.
- Skill and Expertise: Effective threat modeling requires specialized knowledge and expertise in security principles, attack techniques, and risk assessment methodologies. Organizations may face challenges in acquiring and retaining skilled security professionals with threat modeling capabilities.
- Resource Constraints: Conducting thorough threat modeling exercises requires time, resources, and collaboration across different teams and stakeholders. Organizations may encounter challenges in dedicating sufficient resources to threat modeling efforts amid competing priorities and constraints.
- Tooling and Automation: While there are tools and platforms available to support threat modeling activities, organizations may struggle to integrate and automate threat modeling processes effectively within their existing development workflows and toolchains.
Best Practices for Threat Modeling
- Start Early: Begin threat modeling activities as early as possible in the software development lifecycle to identify and address security threats and vulnerabilities before they are embedded in the system architecture or codebase.
- Involve Stakeholders: Engage stakeholders from various roles and disciplines, including developers, architects, security professionals, and business stakeholders, in threat modeling exercises to ensure comprehensive coverage and alignment with organizational goals.
- Adopt Standardized Methodologies: Choose and adopt standardized threat modeling methodologies and frameworks, such as STRIDE, DREAD, or PASTA, to guide and structure threat modeling activities consistently across projects and teams.
- Iterate and Refine: Treat threat modeling as an iterative process that evolves over time based on feedback, lessons learned, and changes in the threat landscape. Continuously refine and improve threat modeling practices to adapt to evolving risks and requirements.
- Integrate with Development Workflows: Integrate threat modeling activities seamlessly into existing development workflows, tools, and processes, leveraging automation and tooling to streamline threat identification, analysis, and mitigation.
Conclusion
Threat modeling is a vital component of cybersecurity and risk management, enabling organizations to identify, assess, and mitigate security threats and vulnerabilities proactively. By adopting a systematic approach to threat modeling and leveraging standardized methodologies, organizations can enhance their security posture, reduce the likelihood and impact of security incidents, and foster a culture of security awareness and accountability.
Connected Agile & Lean Frameworks
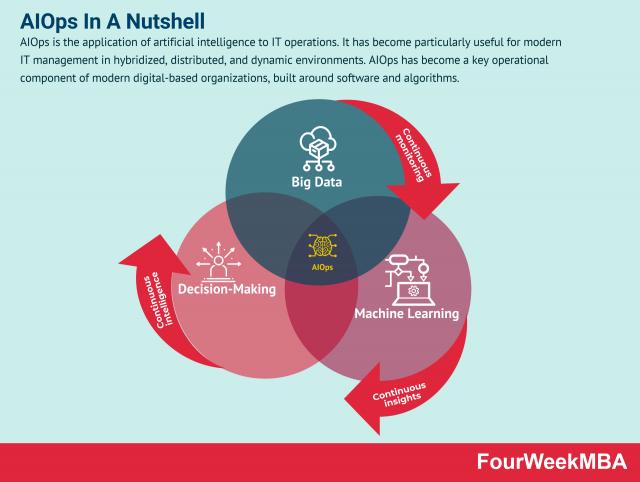
AIOps
AgileSHIFT
Agile Methodology
Agile Program Management
Agile Project Management
Agile Modeling
Agile Business Analysis
Agile Leadership
Andon System
Bimodal Portfolio Management
Business Innovation Matrix
Business Model Innovation
Constructive Disruption
Continuous Innovation
Design Sprint
Design Thinking
DevOps